How Does It Work? Iris Recognition System

Read below about this technology illustrated by a Russian solution — Vzor hardware and software package
Photo: Rostec Electronic Complex
Iris pattern of an eye is unique to each individual. It contains more information that a fingerprint or other biometric identifiers. Pooled analysis of a number of factors makes iris recognition a benchmark in biometric authentication.
Azimuth included in Rostec State Corporation has developed the Vzor systems, Russia’s first iris recognition hardware and software packages: Vzor-Pilon, Vzor-Schityvatel, and Kiosk and Kiosk mini iris pattern recorders.
An ‘ID’ that is always with you
Authentication methods may be divided into three types to be used separately or in various combinations. ‘I have’ methods include access cards, electronic keys, bank cards, etc. Their drawback is in that they can be lost or stolen. ‘I know’ methods include logins and passwords, PIN codes, memorable words, etc., that can be forgotten or hacked. ‘I am’ methods involve biometric identifiers: fingerprints, voice, iris, etc., they are unique and non-transferable. It is biometric identity authentication methods that provide a higher reliability level because these characteristics are unique to each individual.
Keeping an eye
Mathematical statistics currently forms a basis of biometric, and it is the iris pattern interpretation that gives one of lowest errors. This is explained by a high degree of uniqueness of the iris: its structure is formed by the second year of life and remains unchanged. The iris pattern contains many degrees of freedom, which makes this identification method much more accurate than fingerprints and other biometric technologies.

Vzor-Schityvatel. Photo: Rostec Electronic Complex
Where is the technology used?
Iris recognitions may be used in public security systems for ID check, in national ID card systems and biometric passports. In the transport infrastructure, the system has been implemented at the airports in Oman, UAE, USA and United Kingdom. It may be used for providing access to government buildings, data processing centers, nuclear facilities. In the financial sector, the system is used for identity authentication in banking operations. The technology has been also implemented at penitentiaries for identification of prisoners and personnel, for example, at prisons in Turkey.
How does the system work?
Identification process consists of several stages. The first stage is iris pattern recording. It is accomplished by different devices in the Vzor system. The Kiosk records iris patterns automatically, and face, fingerprint and voice patterns, if necessary. Kiosk mini records biometric data. First, a high-resolution infrared camera takes a picture of an eye, then a computer separates the iris from the picture and the image is converted into a unique code.
Initial iris pictures are converted into a closed biometric pattern — a 2 KB binary code. The pattern code is not related in any way to an individual’s personal data, therefore ‘penetration’ into the device memory prevents unauthorized use of biometric data.
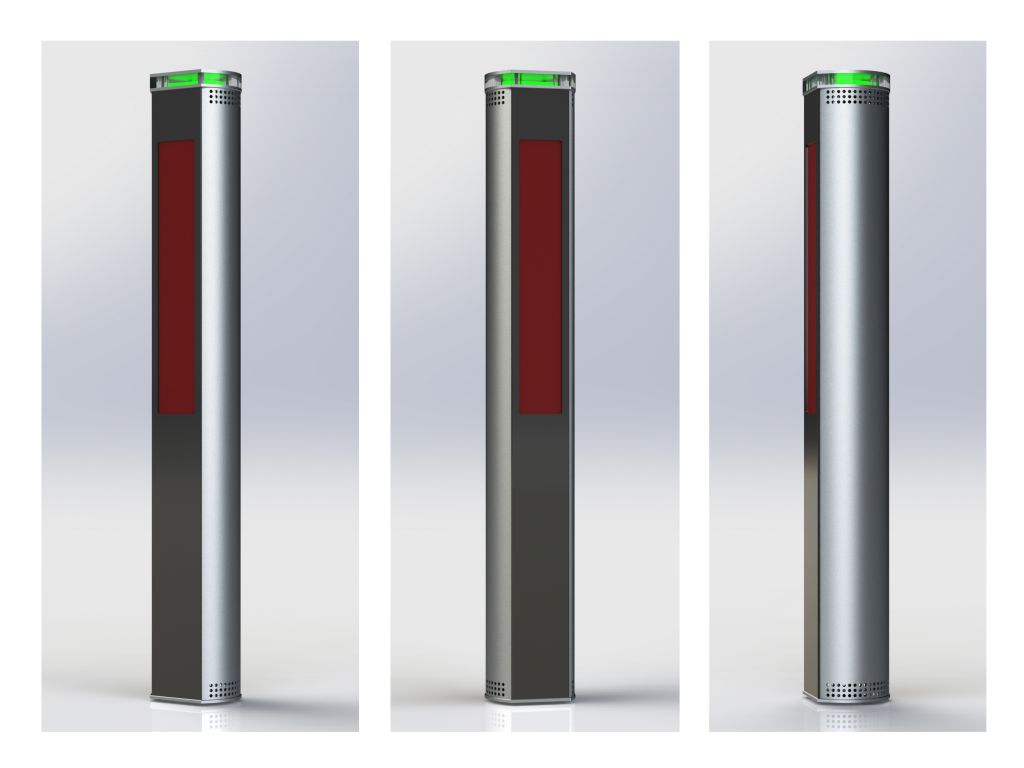
Vzor-Pylon. Photo: Rostec Electronic Complex
The Vzor-Pilon and Vzor-Schityvatel readers are designed for a human identification stage. The Vzor-Pilon is used in high pedestrian activity areas. Options with an effective distance of 1.2m and 1.9m are available and a throughput rate can be up to 40 people per minute.
The devices form an individual’s impersonal ID and transfer it to the access control system via the Wiegand interface. The devices are based on Astra Linux, a Russian operating system.
